Alerts
Backtrace offers an Alert capability that enables teams to be notified at Warning and Critical levels if error reports reach a critical rate. Alerts are configured to trigger a notification for a workflow integration (for example, a message through Slack or a ticket in Jira) when an error group’s count of crashes reaches a specified threshold within a defined timeframe.
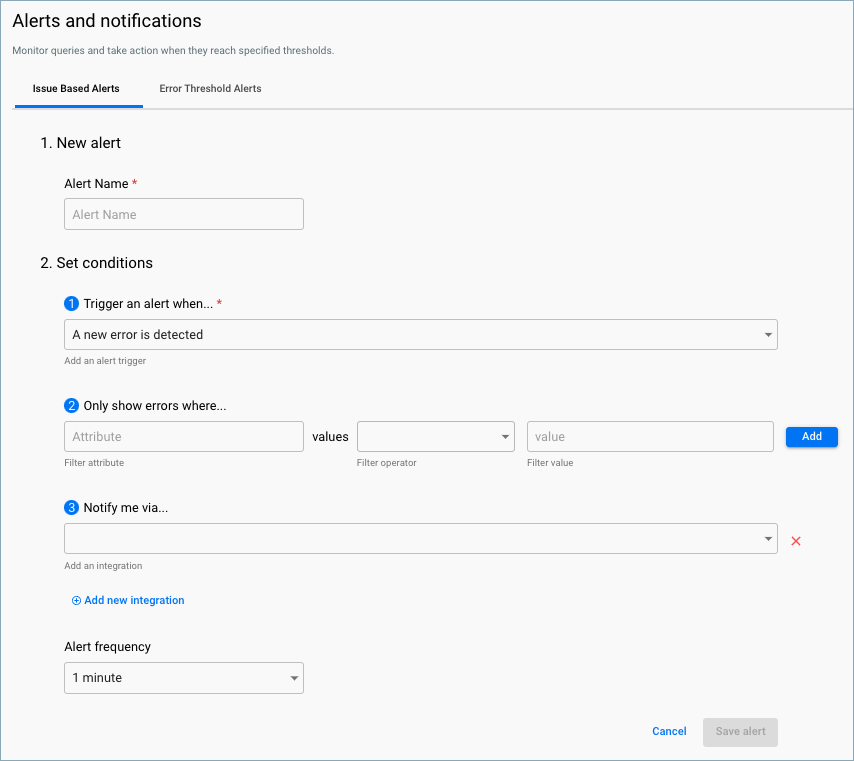
Issue Based Alerts
Use issue based alerts to automatically generate notifications or create issues for your third-party integrations when Backtrace detects a new error or fingerprint in the system. You can specify the conditions and frequency for which alerts are triggered.
Define Alert Conditions
To get started, you must choose whether to be notified with every new error or every new fingerprint. If you have a high volume of errors or are connecting with an issue-tracking system like Jira, it's generally recommended to set triggers for new fingerprints to reduce noise.
Other options are attribute filtering, errors in a timeframe, and affected users in a timeframe.
Alert frequency allows you to control how often an alert will trigger. If you want to send messages for new errors, longer alert frequencies will allow batching of the same error and reduce the overall number of messages.
Error Threshold Alerts
Error Threshold Alerts can be created from the Explore view after applying filters by using Export as:
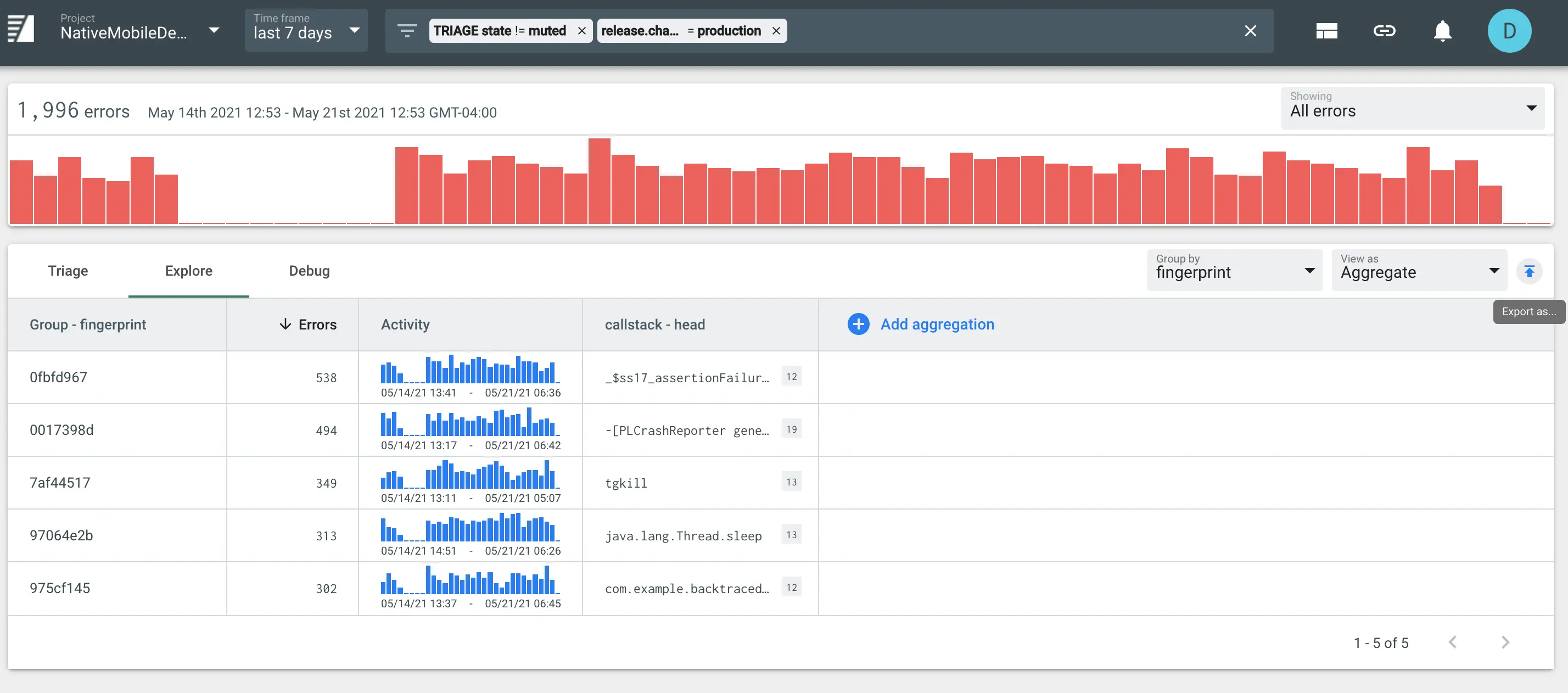
You can configure the alert as follows:
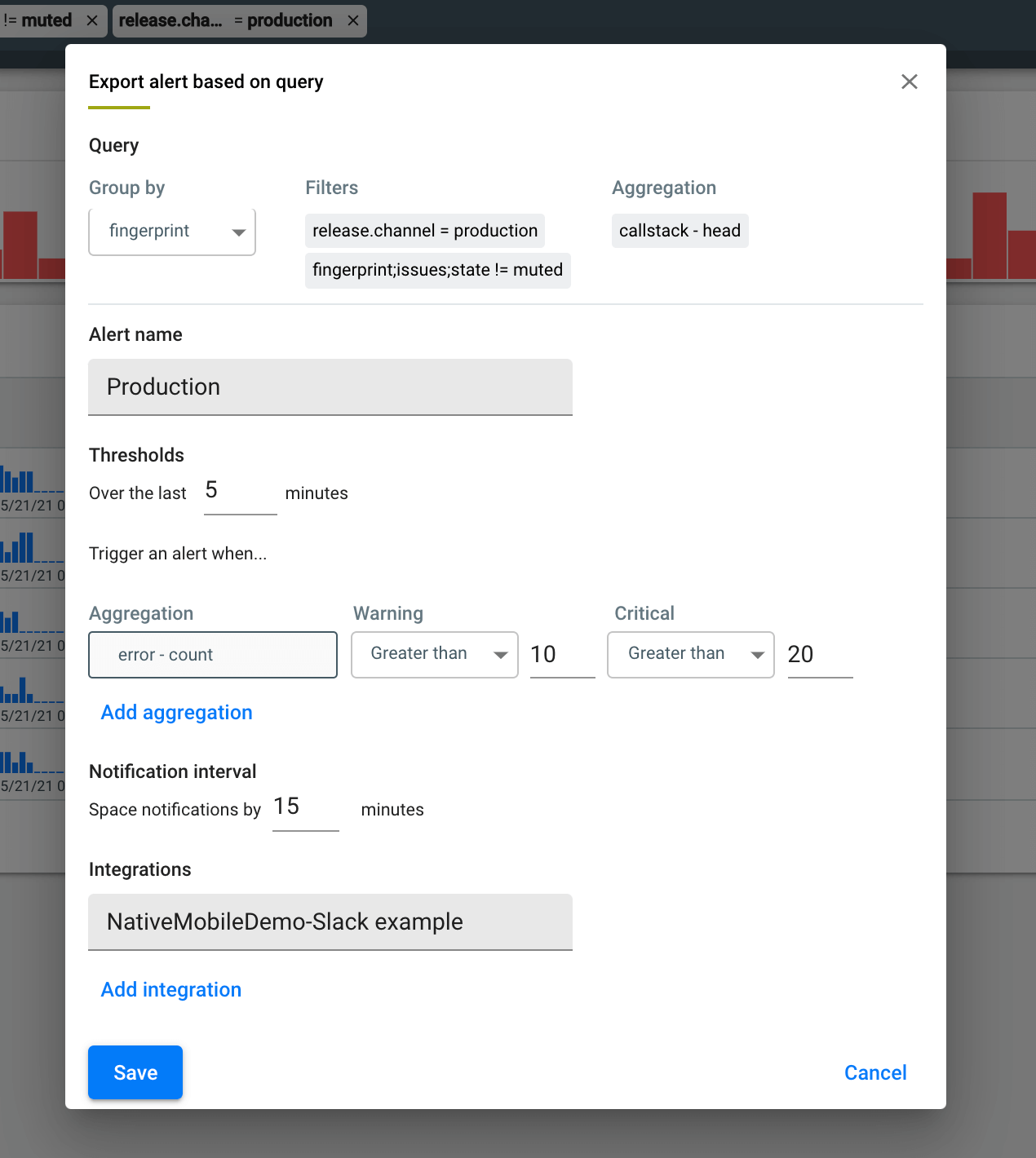
In this example, we are filtering for crashes in the production release channel in non muted fingerprints and grouping by fingerprint. The thresholds are set to fire a warning if any fingerprint within the filter gains 10 new objects within 5 minutes, and a critical alert if any fingerprint within the filter gains 20 new objects within 5 minutes. Alerts will be spaced by the notification interval, set to 15 minutes in this example. The final step in configuring the Alert is selecting a workflow integration for the notification to be sent with.
Once an alert has been saved, its configuration will display under Project settings > Alerts.
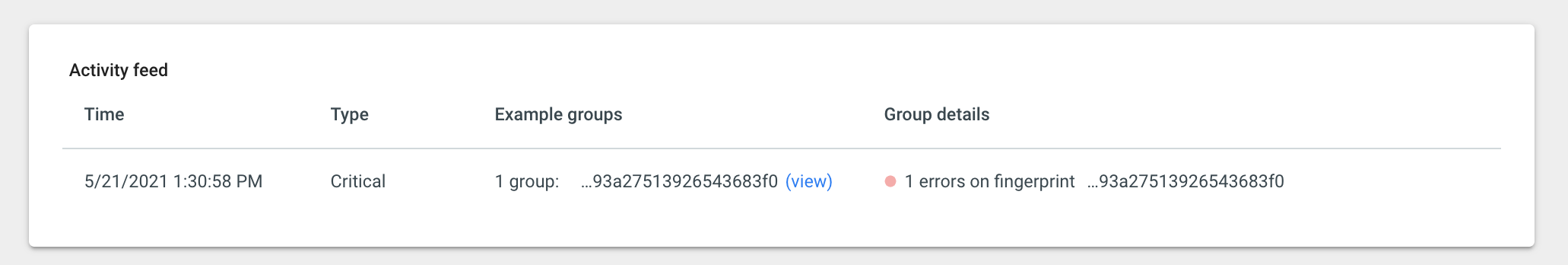
When a threshold is met, a notification including a link to the alert’s Activity feed (under Project settings > Alerts) will be sent to the integration configured.
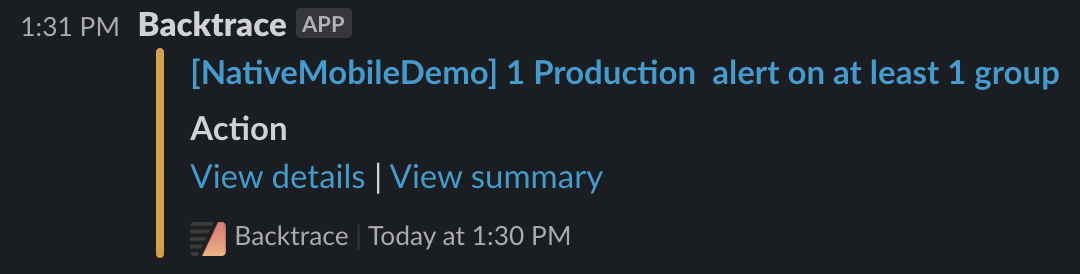
The activity feed will display the fingerprint(s) that met the alert, providing teams with the information they need to investigate the spike.
Alerts can also be created, edited, or deleted from Project settings > Alerts, with the limitation that attribute filters cannot be edited from this endpoint (the explore view must be used for alerts with attribute filters).